TABLE OF CONTENT
Before You Install: Read This First
Most software enters a company quietly. Someone signs up, connects a few apps, and within minutes the tool becomes part of the workflow.
Clawbot doesn’t work that way.
You’re not installing a dashboard, plugin, or chatbot widget — you’re introducing an operational AI agent. It reads information, makes decisions, and can trigger real actions across your systems. The moment it connects to live workflows, the question changes from “Does it work?” to “Can we trust it?”
Many teams rush the setup because the first results look impressive. The agent drafts messages, flags issues, and automates tasks. But problems rarely appear during testing. They appear after trust is granted too quickly. The risk with agentic systems isn’t intelligence — it’s unstructured access.
So installation is not about speed.
It is about controlled introduction.
Fast setup gives a demo.
Structured setup creates a reliable operator.
Start With the Environment, Not the Interface
A common mistake is installing the agent on a personal machine just to try it quickly. That works for communication tools — not for operational AI.
Clawbot accumulates memory: logs, workflow context, tokens, and permissions. If that lives on a laptop or shared environment, exposure becomes invisible. From day one, the system should run inside dedicated infrastructure — a secured server, private cloud instance, or isolated virtual machine.
Treat it like infrastructure early, and you won’t need to rebuild trust later.
Safety Is Defined by Permissions
People assume the AI itself is the danger. In reality, permissions are.
If the agent can access everything, eventually it will use everything — even while trying to help. The correct rollout begins with visibility instead of authority. Let it read before it edits. Let it suggest before it executes. Let automation come last.
Security with AI agents isn’t about limiting capability. It’s about sequencing capability.
Contain the Network, Not the Intelligence
You don’t make an AI safer by making it less capable. You make it safer by controlling where it can act.
A secure installation ensures the agent operates inside a private network and communicates outward only when needed. External systems shouldn’t freely send instructions into it. This means restricted ports, private routing, and controlled gateways.
Think of it as giving an employee a phone — not leaving the office door open.
Human Approval Builds Trust
Autonomy should never be the starting point. It should be earned.
At the beginning, every meaningful action should pass through human review — sending emails, updating records, triggering workflows, or changing data. This prevents costly mistakes and produces feedback that improves reliability.
Teams that skip this stage often mistrust the system later, not because AI failed, but because it was never guided.
Logging Makes the Agent Understandable
If a human employee changes something, you can ask why.
With AI, the record must already exist.
Every decision and action should be logged and reviewable. Observability turns the agent from a black box into an auditable operator. Trust grows when behavior is explainable.
No logs, no confidence.
Separate Learning From Production
Allowing the system to learn directly in live workflows is risky. Training should happen in controlled environments first, then expand gradually into production.
Just like onboarding a new employee — training comes before responsibility.
Stop Planning AI.
Start Profiting From It.
Every day without intelligent automation costs you revenue, market share, and momentum. Get a custom AI roadmap with clear value projections and measurable returns for your business.
Step-by-Step: How to Install Clawbot Safely
Below is a production-grade installation flow. Follow the order — skipping steps is where most failures happen.
1. Create a Dedicated Environment
Prepare secure infrastructure:
Use:
- Private cloud VM (AWS / Azure / GCP)
- On-premise secured server
- Isolated virtual machine
- Docker container in protected network
Avoid:
- Personal laptops
- Shared computers
- Direct local installation
The agent will store tokens, workflow memory, and logs — this must remain controlled.
2. Install Runtime & Dependencies
Inside the server:
- Update system packages
- Install Docker or runtime environment
- Create a non-admin service user
- Configure firewall rules
Now the system can safely host the agent.
3. Deploy Clawbot
Deploy inside a container or isolated service:
- Pull Clawbot package/image
- Create configuration file
- Add environment secrets (API keys, credentials)
- Start the service
Never hardcode secrets.
4. Configure Network Security
Restrict communication:
- Private IP access only
- Reverse proxy or API gateway
- IP allow-listing
- Outbound connections allowed
- Inbound commands restricted
The agent can reach services — services shouldn’t freely reach the agent.
5. Connect Integrations in Read-Only Mode
Connect business systems carefully:
Examples:
CRM, helpdesk, database, Slack, email, dashboards
Start with:
Read → Analyze → Suggest
No write permissions yet.
6. Enable Logging & Monitoring
Before real usage, activate observability.
Log:
- Prompts
- Decisions
- Actions attempted
- API calls
- Errors
If actions cannot be audited, automation should not exist.
7. Add Human Approval Layer
Require confirmation for:
- Sending messages
- Updating records
- Triggering workflows
- External actions
Now the agent behaves like an assistant, not an uncontrolled actor.
8. Run in Sandbox Mode
Test using non-production data.
Let the agent observe workflows and suggest actions.
Review results and adjust permissions.
9. Gradually Allow Actions
Increase authority step-by-step:
- Draft only
- Draft + approval execution
- Limited automation
- Scheduled automation
- Trusted automation
Never jump directly to full automation.
10. Move to Production
After stable performance:
- Connect live data
- Keep approval for critical actions
- Continue logging permanently
Installation is complete only when monitoring is active — not when the system starts.
The Real Security Principle
Traditional systems are secured from attackers.
Agentic systems must also be secured from good intentions.
A helpful assistant acting on incomplete understanding can create more disruption than malicious code. Safe deployment aligns capability with context over time.
Final Thoughts
Clawbot can become one of the most valuable operators in your organization — monitoring processes, handling repetitive decisions, and keeping workflows moving quietly in the background.
But its value depends entirely on how responsibly it is introduced.
Fast installation creates excitement. Careful installation creates reliability.
Need Help Setting It Up Correctly?
Secure AI deployment requires infrastructure design, permission planning, monitoring, and staged rollout — not just technical setup.
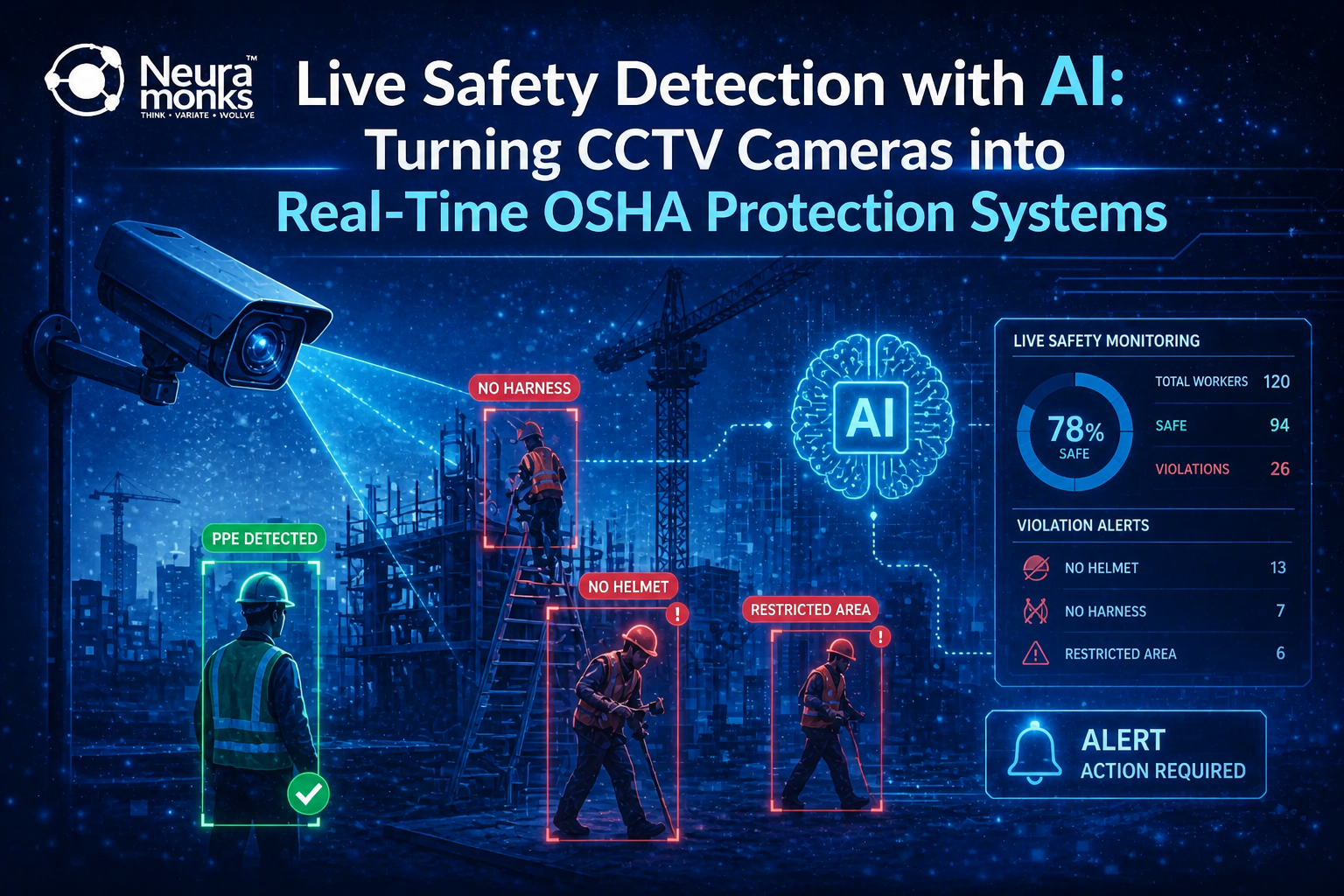
At NeuraMonks, we help organizations deploy production-grade AI operators with governance and safe autonomy expansion.
Because the goal isn’t just to run AI inside your company —
it’s to trust it there.